Researcher Advises Public to Reevaluate Trust in ‘Trusted Systems’
Researcher Patrick Burkart said his goal is to prompt Aggies – and everyone in a leadership position – to critically evaluate the public trust in modern 'trusted systems' that subject consumers' personal data to hacking.
By Madison Brown

Patrick Burkart enjoys an informal dinner gathering during a recent trip to Russia where he was invited to present his research about cyber security and hacking to other researchers.
The public generally agrees the invention of smart phones by trusted systems such as Apple and Android have made daily tasks easier. What the public generally does not know – and likely would not agree to – is when they Venmo a friend or order an Uber, they have entrusted the security of their phones and their personal data to companies that put it at risk of hacking.
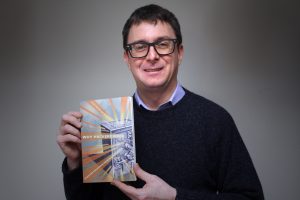
In his new book Why Hackers Win: Power and Disruption in the Network Society, Patrick Burkart, Ph.D., challenges his audience to reconsider the trust they hold in trusted systems. Together with co-author Tom McCourt from Fordham University, Burkart has distilled his research to explain how hacking and hacking tools are legitimized, legal and even promoted as problem-solving instruments by businesses and the government. The studies compiled in Why Hackers Win demonstrate how tools for hackers are increasing in power and availability with little to no repercussions for the business, but with potential harm for the user, said Burkart.
In October, Burkart was invited to lead seminars in Russia and Finland on Why Hackers Win for other researchers studying hacking and cyber security. Closer to home, Burkart said his goal is to prompt Aggies – and everyone in a leadership position – to critically evaluate the public trust in modern “trusted systems.”
The term “trusted systems” is defined as systems created by companies for exchanging payments for services or ostensibly for securing and restricting access to accounts, Burkart said. Although legally protected from hacking, those protections can be weak and sloppily defended without recourse to victims whose accounts have been hacked, he added.
“We cannot avoid the technology systems we have set up for modern life,” said Burkart. “If we know these systems are inherently at risk of being manipulated, our legal system is ill equipped to handle those manipulations, and the economic system is actually promoting the manipulation of those systems … then we should be assessing our comfort levels with the trusted systems that we are asked to trust.”
Burkart’s research area is media, law and policy. He looks at hacking from a law perspective and from a business perspective, as well.
“I want to not just look at what the law says, but what are the implications of what the laws says,” explained Burkart. “I want to not just say ‘How are people doing business in these markets with hacking, anti-hacking, piracy or anti-piracy?’ but why things are done this way and why are these viable practices.”
Why Hackers Win takes an in-depth look at how companies use hacking to advance their business objectives.
 “[The book] looks at examples where very large companies that should know better – and even our own government – are abusing the trust of their technology systems even while they are trying to persuade their customers to buy into these systems and put their trust in them,” said Burkart.
“[The book] looks at examples where very large companies that should know better – and even our own government – are abusing the trust of their technology systems even while they are trying to persuade their customers to buy into these systems and put their trust in them,” said Burkart.
Burkart points to Uber as a major company guilty of using hacking techniques to advance business growth based solely on Uber’s own questionable terms. Uber’s apps have been used to spy on Uber drivers – and on their customers.
“They have developed software that spies on their drivers and reports when they go to drive for another transportation company like Lyft, for example,” explained Burkart. “They use hacking techniques to promote anticompetitive business practices and also to surveil their customers.”
When Burkart was invited to Tampere, Finland, he said fellow researchers wanted to discuss their concerns about potential manipulation of public opinion by the Russian government in European elections.
“They were very interested in my new book particularly because they think that the problems with cyber security, foreign interventions and political regimes are very closely related phenomena,” said Burkart.
Burkart said his book speaks to everyone’s day-to-day interactions with technology, not just to other researchers.
“There is a lot of good, practical wisdom in this book,” said Burkart. “Particularly for decision makers like we know Aggies are going to be when they graduate and move on to positions of responsibility.”
Why Hackers Win: Power and Disruption in the Network Society is available through the University of California Press.
- Dept News
- Faculty
- In the Department
- Research
- Co-author
- COMM
- Communication
- Cyber Security
- Department of Communication
- Dr. Patrick Burkart
- Faculty
- FInland
- Fordham University
- Hacked
- Hacker
- Hackers
- Hacking
- In the News
- Law
- law and policy
- media
- Media and Law
- Patrick Burkart
- Patrick Burkart Ph.D.
- Piracy
- Policy
- Russia
- TAMU
- TAMU Author
- TAMU COMM Department
- Technology
- Texas A&M Author
- Tom McCourt
- Why Hackers Win
- Why Hackers Win: Power and Disruption in the Network Society
- Writing
